Tldr it's used to make initial GPS fix faster by getting satellite positioning information.
Not a fan of how they say "we didn't say it's a backdoor," but have "secretly share" in the URL and article title.
A backdoor would imply some sort of external control I'd think, a much broader potential for harm.
Being able to command a device to send you info or perform tasks is different than the device sending info of its own accord.
A backdoor would imply some sort of external control I'd think...
Yes, technically a backdoor listens: https://csrc.nist.gov/glossary/term/backdoor
Being able to command a device to send you info or perform tasks is different than the device sending info of its own accord.
In this context, where it's implied to send without the owner's knowledge (ignoring the fact it's documented), not really. The article screams "gotcha!" when in reality it didn't, so they're trying to backtrack and downplay their initial response. But I do appreciate their update, it's just got a PR spin to it.
Edit: if the article was initially written as more of a "did you know" and/or expanding on existing documentation, wouldn't be an issue. It's the "it's secretly stealing" that implies malice which is part of the definition of malware... that'shares a category with backdoor. So splitting hairs in the name of PR.
there is an important difference between sending data and accepting remote control
That's a good read, especially the additional context at the bottom of the article.
After a quick search: Izatcloud is qualcomm extended satellite positioning, which may be a different version of GPS. But not entirely sure, here is a privacy related article about it. https://restoreprivacy.com/qualcomm-denies-unlawful-user-location-data-collection-on-phones/
@AlbinJose1001 base host appears to be some location provider from Qualcomm? http://izatcloud.net/
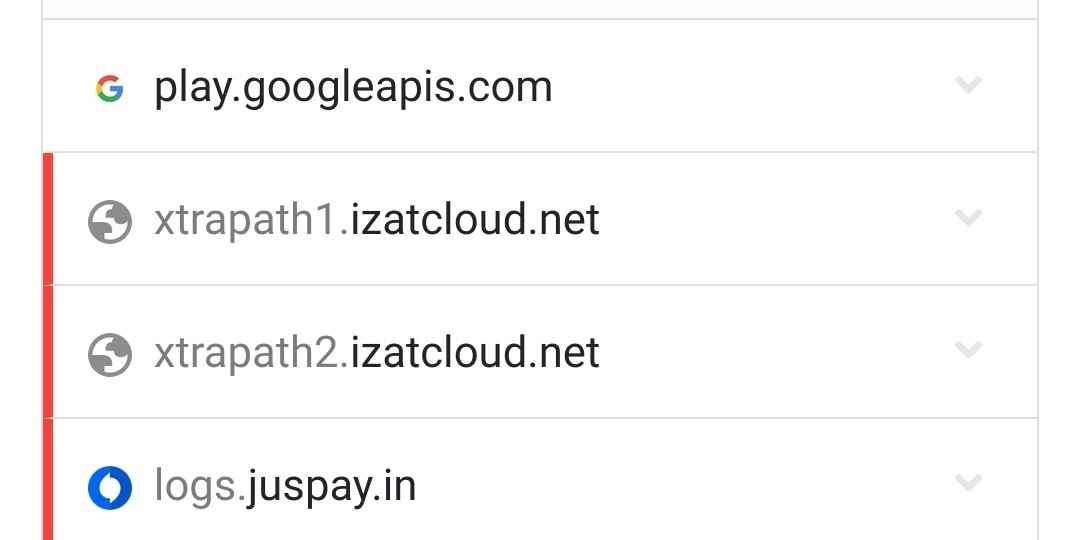
I don't know. My xiaomi device is making crazy amount of connections to.... Xiaomi.net, Xiaomi.com, Miui.com, idmb-app-chat-global-xiaomi10-407281533.ap-south-1.elb.amazonaws.com And now... xtrapath1.izatcloud.net
As others have said, manufacturer telemetry. Just the usual built-in spyware that people are fine with for some reason... Everyone does it, they're just bad at hiding it in this case.
As mentioned, this is a Qualcomm thing. Not exactly spyware, but probably not necessary either.
https://www.qualcomm.com/site/privacy/services
Qualcomm Location Service (formerly “IZat Location Services” or “IZat”) is technology offered by Qualcomm Technologies, Inc. in the U.S., QT Technologies Ireland Limited in countries within the European Economic Area, and Qualcomm CDMA Technologies (Korea) YH in the Republic of Korea (a.k.a. South Korea). Qualcomm Location Service may enable your device to determine its location more quickly and accurately – even when your device is unable to get a strong GPS signal.
Something like the UAD could disable it, or you could use Tracker Control to block it, or straight up use adb to disable it... But, it will run even if disabled.
The package is com.qualcomm.location so,
adb shell pm uninstall --user 0 com.qualcomm.location
will disable it, but it will always come back...
Removing it can cause a bootloop in some cases, likely something in the boot process is looking for it and reinstalling that app if missing. Google's play services recently started doing that with permissions that are revoked with root
Should be removable on a non-stock ROM though
I asked very similar question here.
https://lemmy.world/post/7424307
The address is diffrent because you have older phone.
Is *.xtracloud.net related? I found it in my logs.
Yes it absolutely is. It’s also Qualcomms.
Yes, it's the newer version of the two. OP has an older device
Yeah, It's izatcloud.net related.
Privacy Guides
In the digital age, protecting your personal information might seem like an impossible task. We’re here to help.
This is a community for sharing news about privacy, posting information about cool privacy tools and services, and getting advice about your privacy journey.
You can subscribe to this community from any Kbin or Lemmy instance:
Check out our website at privacyguides.org before asking your questions here. We've tried answering the common questions and recommendations there!
Want to get involved? The website is open-source on GitHub, and your help would be appreciated!
This community is the "official" Privacy Guides community on Lemmy, which can be verified here. Other "Privacy Guides" communities on other Lemmy servers are not moderated by this team or associated with the website.
Moderation Rules:
- We prefer posting about open-source software whenever possible.
- This is not the place for self-promotion if you are not listed on privacyguides.org. If you want to be listed, make a suggestion on our forum first.
- No soliciting engagement: Don't ask for upvotes, follows, etc.
- Surveys, Fundraising, and Petitions must be pre-approved by the mod team.
- Be civil, no violence, hate speech. Assume people here are posting in good faith.
- Don't repost topics which have already been covered here.
- News posts must be related to privacy and security, and your post title must match the article headline exactly. Do not editorialize titles, you can post your opinions in the post body or a comment.
- Memes/images/video posts that could be summarized as text explanations should not be posted. Infographics and conference talks from reputable sources are acceptable.
- No help vampires: This is not a tech support subreddit, don't abuse our community's willingness to help. Questions related to privacy, security or privacy/security related software and their configurations are acceptable.
- No misinformation: Extraordinary claims must be matched with evidence.
- Do not post about VPNs or cryptocurrencies which are not listed on privacyguides.org. See Rule 2 for info on adding new recommendations to the website.
- General guides or software lists are not permitted. Original sources and research about specific topics are allowed as long as they are high quality and factual. We are not providing a platform for poorly-vetted, out-of-date or conflicting recommendations.
Additional Resources:
- EFF: Surveillance Self-Defense
- Consumer Reports Security Planner
- Jonah Aragon (YouTube)
- r/Privacy
- Big Ass Data Broker Opt-Out List