6.75 bottles
Ponziani
Looks good, how sweet versus tart was it?
Do it and share it with friends and family! You will never regret it. Once you start and get the hang of things it's easy and flexible.
Ok thank you!
Im a little knowledgeable with this stuff but i do not know how to see the "handshake" itself, but maybe this is synonymous with what i am doing:
Right click any of the packets (TCP or SSH) > Follow > TCP stream
From there i can see some info about the ssh protocol and connection, as well as the 2 devices communicating (Operating systems used) followed by random gibberish which is the encrypted data.
When I analyze the TCP packet "frames", they contain data including the motherboard manufacturer, but packets themselves look like its just gibberish.
Thanks by the way for trying to help me :)
It looks like everything is in 1 stream, maybe that answers your question? I am capturing traffic only on port 22 briefly while the rsync is running to look at the packets
The only thing missing is a random arrow
Only way is to run to Lichess
I figured its another black box hell like a google meets or something similar where itll try to grab any detail, data or info about what i am connecting with, and also how trustworthy the E2E encryption is if its proprietary
Thank you both
Awesome now I understand what you and the other commenter were talking about with aliasing. Well this works perfect without the alias, many thanks


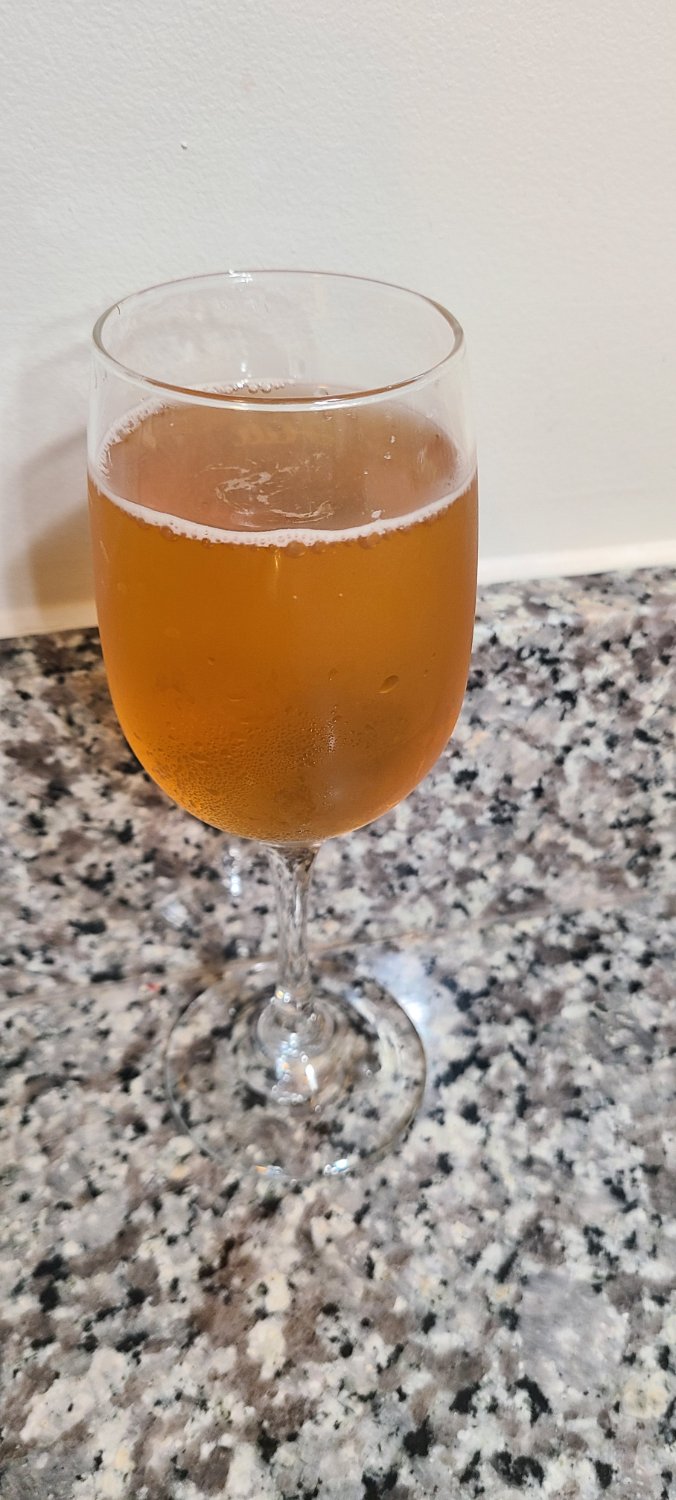

I let them go for 1-2 weeks before refrigeration which seems to be longer than most people, but i like strong carbonation so i aim to over do it vs under do it.