The best ones show a port scan. The worst just show scrolling html source code.
Trinity used NMAP and scanned for real known SSH vulnerabilities when hacking the power station in Matrix Reloaded.
The legendary ones show a "BREACH" at the target systems, in Red Bold Times New Roman font size 150.
Extra point if they have the PowerPoint shuttle controls visible in the bottom-left corner.
A serif font on a computer display?! Appalling! Sacrilegious!
The Dark Side of the Force is a pathway to many abilities some consider to be…unnatural.

Go watch Mr Robot, it's great and does not do this
Been meaning to!
I am not a programmer by any means but I know enough to know they did their research.
Except Tyrell called it "nome" instead of "g'nome" and I'm pretty sure TOR exit nodes can only see unencrypted data and the entry node can only see who sent it.
Never forget the infamous NCIS co-op hacking on a keyboard scene.
I remember a scene of such a crime movie that was at least funny for people used to computers and progrmmers.
The (old and seasoned) detectives were brought in contact with the new "cyber unit" of the police. Stored away in an otherwise empty office floor somewhere, they were the absolute movie style hackers: cluttered desks, sloppy outfit, beards. The old detectives were quite reluctant to work with those young "computer people" and had a lot of prejudices. Then, one of the detectives found a big red button on the desk and said "I wonder what happens when I press this button" - and presses it. And the "cyber guys": "DON'T!". The detective mocks them, and presses the button several times before he asks what the button actually does. Cyber guy: "That is our 'order pizza' button! I hope you've got enough money to pay for this...". Cut. Next scene: They are all eating pizza together from a desk-high stack of pizza boxes.
You know, I've seen this dozens of times but I'm just realizing, at least assuming that's not a power bar (which would be odd since it matches the plug of the monitor or PC), since the monitor shut of straight away, he actually only unplugged the monitor. The PC should still be on and getting hacked.
Yes, my favorite comment:
pulls out the power cord for the monitor
Job done!
followed by:
Attacker must have had 5 people on the keyboard.
If it's even that. Most of the time it's non-nonsensical gibberish.
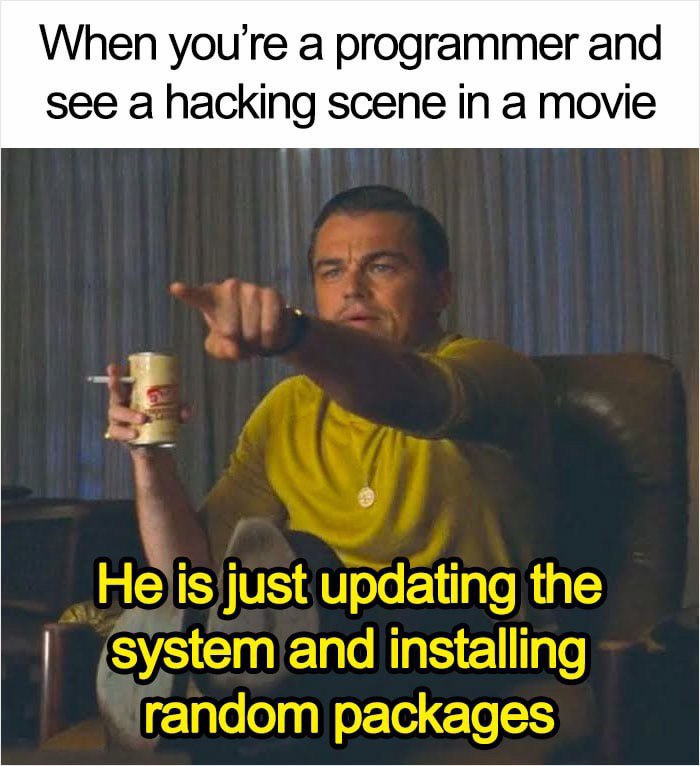
I was watching a show recently where someone was writing code, and it was actually C++ code. I actually did the exact pose in the meme.
Of course, he was writing it inhumanly fast, and he always seemed to be writing the start of a new file. But I liked that it was actually code and not just The Matrix-style jibberish
When I made a short film about an AI I was writing C# into visual studio as my coding. It was actual video game code that was for something like AI pathfinding or something, so I tried to make it somewhat accurate.
Not sure why movies can't spend a grand on a programing consultant to actually write them some hacking-ish code for the scenes.
My guess is that they just don't care to spend the time on it when the majority of people wouldn't even notice. But of course those of us that would notice would really appreciate it.
As a guitar player, it equally irritates me when the person "playing" the guitar has clearly never touched a guitar in their life. Similarly, when an actor is actually playing it, I really appreciate it.
Off topic, but I once walked in while my wife was watching some anime where the guitars were all extremely accurate, like down to what tuning pegs they would have had for the era the guitars were from. They must have motion captured all of the guitar playing from when they recorded the music, or at least took video of their hands, because they animated it perfectly. Down to the tapping parts and everything. It was jaw dropping. I made her start the whole show over from episode one so I could watch it.
The show Mr. Robot did that, they used real 0-day exploits for their hacking scenes!
Sounds like hackertyper.net
That's likely exactly what it was.
sudo apt-get install hackerman
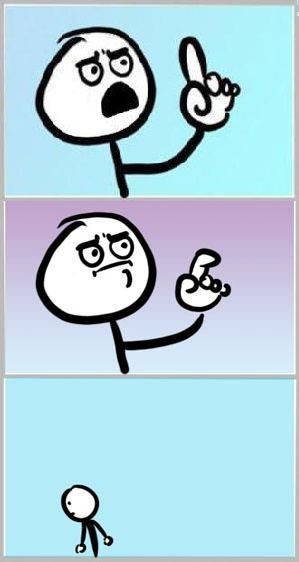
You actually don't need the -get anymore
It's recommended for script usage
What if jumping off a bridge was recommended for script usage?
Easy, export BRIDGE_BEHAVIOR=legacy and pretend nothing changed until everything one day breaks horribly in production.
sees them using Assembly
okay this probably doesn't make sense but I'm too lazy to prove it
Don't forget the ridiculous amount of beeping and other sounds when characters fly over the screen at twice the speed of light!
He is building Firefox from source, don't worry
As an actress, that's nonsense, if hacking scenes in movies are fake, then how do you explain this documentary I watched where this hacker man hacked a kung fu fighting cop back in time to kill Hitler (and David Hasselhoff was there for some reason, too)?
Do we have a "itsaunixsystem" community here?
Wait, you guys don't update your system and install random packages before going on a hacking spree?
What have I been doing all this time?
Probably masturbating
Running "top" is also some common thing.
So, when I got a bunch of free serial WYSE terminals ages ago, I propped them up on the shelf, daisy-chained them, wrote a wrapper to be able to address all four screens through one UART, and had them display (and regularly update) system stats. Just because.
I recently started rewatching Gundam Wing, and one of the computer screens with fast scrolling text was just scrolling through the Readme of either old Adobe Software or old Printer software (I don't remember which).
Dark mode.
It's almost always just htop and/or hackertyper and/or the fancy matrix effect
Try being a medical biologist watching outbreak/pandemic films. It's fucking painful to watch.
I thought the bash history in tron: legacy was kind of clever. There was stuff like vi last_will_and_testament.txt before the computer ducking command. I remember being surprised some prop designer knew enough about computers to set up that easter egg. Although I think I was reading that they contracted out the design of the OS to some team or something.
This always makes me laugh (IRC): https://www.youtube.com/watch?v=O2rGTXHvPCQ
Funnily enough I have to hide terminal windows when updating while I'm around any of my less tech savy friends who think it's scary or creepy. I really dislike them portraying this as "hacking".
I think that most of the time even if they know what it would look like in the real world, movie creators intentionally make it look silly - I guess mostly for the entertainment value, or as kind of a joke in the lines of "let's see how absurd we can make it before your grandma notices something's not right".
Programmer Humor
Post funny things about programming here! (Or just rant about your favourite programming language.)
Rules:
- Posts must be relevant to programming, programmers, or computer science.
- No NSFW content.
- Jokes must be in good taste. No hate speech, bigotry, etc.